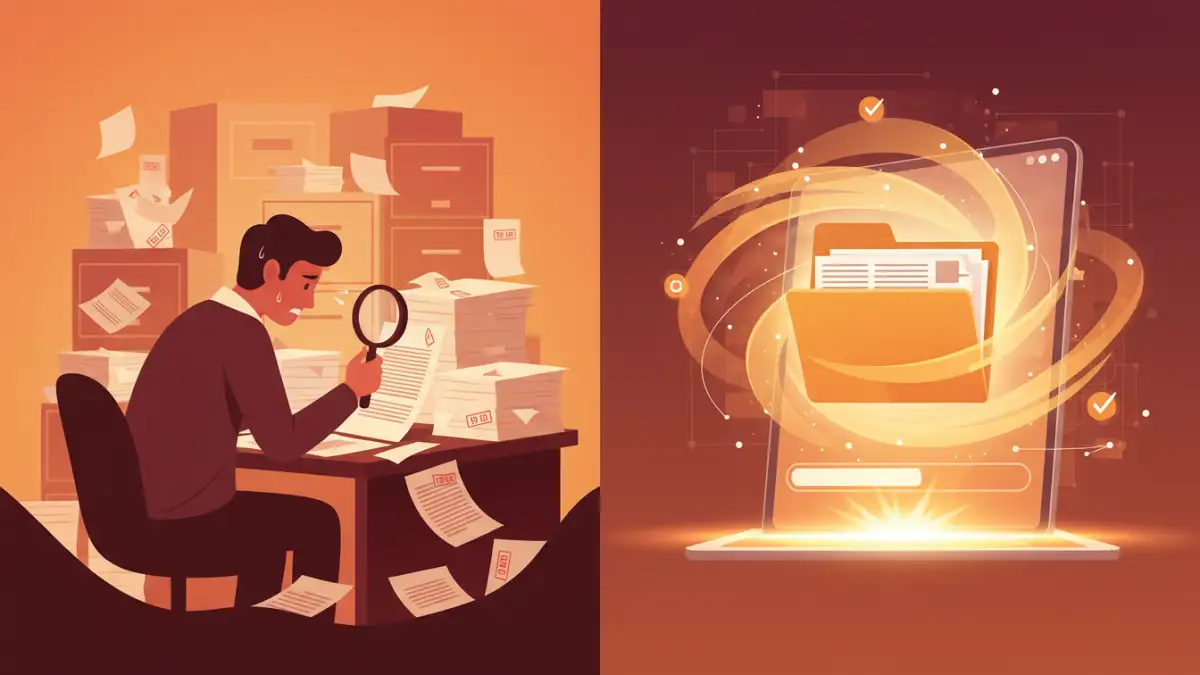
When you're faced with a folder full of sensitive documents that need to be shared or archived securely, the thought of individually encrypting, compressing, or applying security settings to each file can be daunting. This is a common challenge for professionals across many industries, from legal and finance to healthcare and education. I've seen firsthand how time-consuming this process can become, often leading to errors or rushed security measures.
Fortunately, there are efficient ways to handle this. By employing batch processing techniques, you can significantly speed up the process of securing multiple files simultaneously. This not only saves valuable time but also ensures a consistent level of security across all your documents.
Table of Contents
Understanding the Need for Batch Optimization
The primary driver for batch optimization is workflow efficiency. Imagine needing to send a proposal with multiple supporting documents to a client, or archiving years of financial records. Doing this one by one is not only tedious but also prone to human error. A consistent security policy applied to all files is crucial.
Why Batch Processing Matters
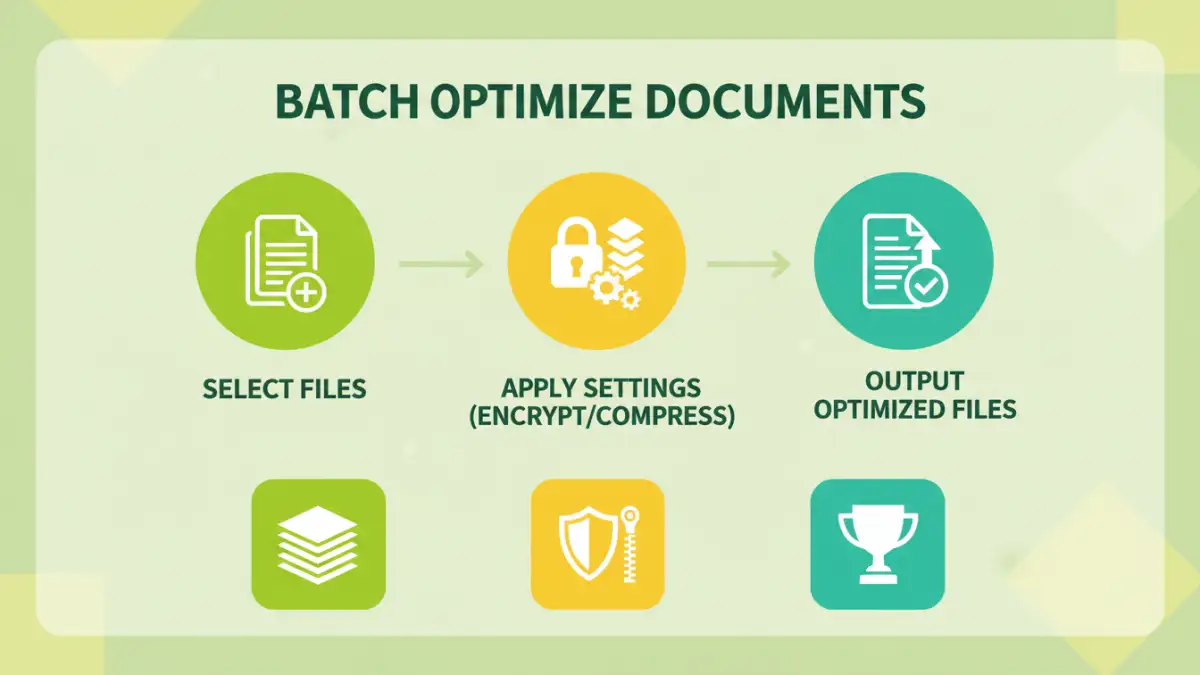
Batch processing allows you to apply the same set of actions—like encryption, compression, or watermarking—to a large number of files at once. This is particularly useful when dealing with different file types such as PDFs, Word documents, or spreadsheets, ensuring they all meet your security standards before distribution or long-term storage.
Practical Methods for Batch Optimization
Several approaches can help you achieve batch optimization, depending on your technical comfort level and the tools available. These methods range from simple built-in operating system features to specialized software.
Using Desktop Software
Dedicated PDF editors or document management software often come with robust batch processing capabilities. Tools like Adobe Acrobat Pro, Foxit PhantomPDF, or even more specialized utilities allow you to select multiple files and apply actions such as password protection, watermarking, or even bulk pdf compression. I often recommend these for users who regularly handle large volumes of documents, as they offer the most control and features.
Leveraging Online Tools and Scripts
For less frequent tasks or when you need a quick solution without installing software, numerous online tools offer batch processing for PDFs, like merging or splitting. Some advanced users might even script solutions using tools like Python with libraries like PyPDF2 or reportlab for custom batch optimize documents workflows, especially for automating repetitive tasks in larger projects.
Key Considerations for Secure Sharing
When preparing documents for sharing, several factors beyond just encryption come into play. You need to think about the recipient's ability to access the files and the overall security posture.
File Size and Accessibility
Often, batch optimize documents also involves reducing file sizes through compression. This is crucial for email attachments and faster uploads/downloads. However, ensure that the compression method doesn't degrade the quality of important information, especially for image-heavy documents or scanned PDFs. Balancing security with accessibility is key.
Advanced Workflow Integrations
For businesses and power users, integrating batch document optimization into existing workflows can yield significant productivity gains. This often involves scripting or using more advanced features of document management systems.
Automation and Scripting
For those comfortable with command-line interfaces or scripting languages, tools like Automator on macOS or PowerShell on Windows can be used to create custom batch processes. Combining these with file manipulation libraries allows for highly tailored solutions for multiple file optimization, which can be scheduled or triggered by specific events.
Best Practices for Document Security
Regardless of the method chosen, adhering to best practices ensures that your documents remain secure and accessible only to authorized individuals. Consistent application of security measures is paramount.
Always use strong, unique passwords for encryption, and consider using password managers to keep track of them. Regularly update your software to patch any security vulnerabilities. If sharing sensitive data, verify the recipient's identity and ensure they have the necessary tools and knowledge to handle the secured files. Implementing a clear document retention and disposal policy is also part of a comprehensive security strategy.
Comparison Table: Document Security Methods
| Method | Pros | Cons | Best For |
|---|---|---|---|
| Desktop Software (e.g., Adobe Acrobat Pro) | Comprehensive features, high control, reliable batch processing, no privacy concerns | Often requires paid license, can have a learning curve | Regular users, large volumes, complex security needs |
| Online PDF Tools | Accessible anywhere, no installation, often free for basic tasks | Potential privacy/security risks (uploading sensitive data), limited features for batch operations | Quick, simple tasks, non-sensitive documents |
| Scripting (e.g., Python) | Highly customizable, full automation, can integrate into complex workflows | Requires programming knowledge, time investment for setup | Automating repetitive tasks, advanced users, developers |
| Built-in OS Tools (e.g., Automator) | Free, integrated into the OS, good for basic repetitive tasks | Limited functionality compared to dedicated software, OS-dependent | Basic file renaming, simple batch operations on macOS |