
Securing sensitive documents for a growing organization presents a unique set of challenges. It's not just about applying a password; it's about ensuring that your chosen method can handle thousands, or even millions, of files without becoming a bottleneck or a management nightmare. This often leads to a critical question: how do different PDF encryption solutions truly stack up when it comes to scalability?
From my vantage point, having navigated complex data security landscapes for over a decade, I've seen firsthand that a solution that works perfectly for a small team can crumble under the weight of enterprise-level demand. The true test of any security measure, especially for document encryption, lies in its ability to grow and adapt with an organization's increasing needs.
Table of Contents
Understanding the Core Challenge of Scalability
When we talk about the scalability of PDF encryption solutions, we're not just discussing how fast a single file can be encrypted. We're looking at the entire lifecycle: initial encryption, key management, access control, decryption, and auditing across a vast and potentially distributed document repository. This involves processing power, network bandwidth, and the administrative overhead of managing keys and permissions for countless users and documents.
A poorly chosen solution can lead to significant operational costs, delays in document access, and even security vulnerabilities if administrators are forced to cut corners to keep up with demand. The goal is to find a system that not only protects data effectively but also integrates seamlessly into existing workflows without creating new bottlenecks.
Defining Scalable Encryption
Scalable encryption, in this context, means a system's ability to maintain performance and manageability as the volume of encrypted PDFs, the number of users accessing them, and the complexity of access policies increase. It implies efficient resource utilization, automated processes, and robust key management infrastructure. For instance, a solution might be scalable in terms of processing speed but fall short in its ability to manage granular access permissions for thousands of unique documents and users.
True pdf encryption scalability considers not just the technical throughput but also the human element of administration and user experience. If a system becomes too cumbersome to manage, it risks being circumvented, which defeats its entire purpose.
Different PDF Encryption Architectures Compared

Various approaches exist for applying and managing PDF encryption, each with its own implications for scalability. Understanding these architectures is key to making an informed decision for your organization.
Client-Side Desktop Software
Many organizations start with client-side desktop software, like Adobe Acrobat Pro, to encrypt PDFs. This method gives users direct control over individual files, which can be sufficient for small teams or ad-hoc tasks. However, its scalability is inherently limited; each user encrypts files locally, and there's no centralized management of keys, policies, or audit trails. Managing thousands of password-protected documents created this way becomes a chaotic task, relying heavily on individual user discipline.
Server-Side Solutions and Document Management Systems (DMS)
For larger organizations, server-side solutions or integrated DMS platforms offer a more robust approach. These systems can automatically encrypt PDFs upon creation or upload, apply policies based on document classification, and manage encryption keys centrally. Solutions like Microsoft SharePoint with integrated IRM (Information Rights Management) or dedicated document security platforms can process large volumes of files and enforce consistent policies across the enterprise. This approach significantly improves pdf encryption scalability by centralizing control and automating much of the encryption workflow.
Cloud-Based Encryption Services
Cloud-based services provide another avenue, leveraging the cloud's inherent scalability. These platforms often offer APIs for integration, allowing applications to encrypt and decrypt PDFs on demand without managing the underlying infrastructure. While convenient and highly scalable in terms of processing, organizations must carefully evaluate the security posture and data residency policies of the cloud provider. The key management aspect is often handled by the service, which can be both a pro (less administrative burden) and a con (less direct control).
Key Factors for Evaluating Scalability
When assessing the scalability of any PDF encryption solution, several factors come into play beyond just raw processing speed. Neglecting any of these can lead to unexpected challenges down the line.
Performance and Throughput
This is the most obvious factor. How many PDFs can the system encrypt or decrypt per minute? Does performance degrade linearly or exponentially with increased load? For high-volume environments, parallel processing capabilities and efficient algorithms are critical. I've observed that solutions with poor indexing or inefficient cryptographic operations can quickly become a bottleneck, even with powerful hardware.
Key Management and Access Control
Centralized, automated key management is paramount for scalable pdf encryption. Manual key distribution and revocation for hundreds of thousands of documents are simply unfeasible. A robust solution provides secure key storage, automated key rotation, and granular access control mechanisms that integrate with existing identity management systems (like Active Directory or LDAP). The ability to quickly revoke access or change permissions across a large dataset is a non-negotiable aspect of effective security scaling.
Integration Capabilities and Automation
A truly scalable solution shouldn't operate in a silo. It needs to integrate seamlessly with existing business applications, document workflows, and archival systems. APIs, SDKs, and connectors are essential for automating encryption and decryption processes, ensuring that security measures don't disrupt productivity. The less manual intervention required, the more scalable the solution becomes from an operational perspective.
Real-World Scenarios and Practical Solutions
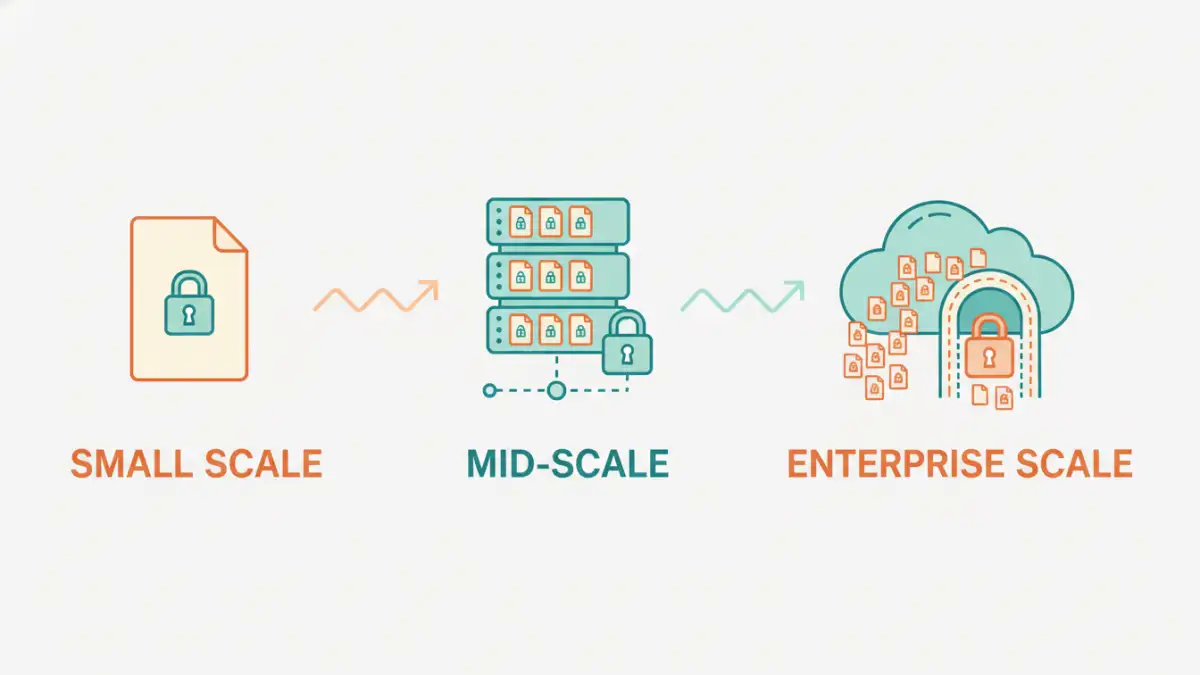
Let's consider how different scenarios demand varying levels of pdf security scaling and which solutions are best suited for them.
Small Business with Occasional Sensitive Documents
A small law firm might only need to encrypt a few dozen client contracts each month. For them, client-side desktop software like Adobe Acrobat Pro, often already part of their toolkit, might suffice. The administrative burden is low, and the cost is minimal. This doesn't require complex scalable pdf encryption solutions, as the volume is manageable.
Mid-Sized Enterprise with Growing Document Repository
A financial services firm generating thousands of statements and reports daily needs a more robust approach. A server-side DMS with integrated encryption capabilities would be ideal. This allows for automated encryption based on document type, centralized policy enforcement, and efficient management of access rights. It addresses the need for comparing encryption tools that offer both security and operational efficiency at scale.
Large Corporation with Global Operations
A multinational corporation handling millions of documents across various departments and geographical locations requires a highly sophisticated, cloud-native or hybrid solution. This might involve a combination of server-side encryption with cloud-based key management services, robust APIs for integration with custom applications, and advanced auditing features. The focus here is on maximum pdf security scaling, global policy consistency, and disaster recovery capabilities.
Best Practices for Scalable PDF Security
Implementing a scalable PDF encryption solution goes beyond just selecting the right software; it involves strategic planning and ongoing management.
- Centralized Key Management: Always prioritize solutions that offer robust, centralized key management. Decentralized keys are a recipe for security incidents and operational chaos as you scale.
- Automate Everything Possible: From encryption on creation to access revocation, automation reduces human error and ensures consistency. This is critical for efficient pdf security scaling.
- Integrate with Existing Systems: Ensure your encryption solution can talk to your DMS, IAM, and other critical systems. Seamless integration minimizes friction and improves adoption.
- Regular Auditing and Monitoring: Implement continuous monitoring of access logs and encryption status. This helps in identifying potential vulnerabilities or compliance issues early.
- Plan for Disaster Recovery: Ensure that your encryption keys and encrypted documents are included in your disaster recovery plan. Losing access to keys means losing access to your data.
- User Training: Even with the most advanced systems, user awareness is crucial. Educate users on the importance of document security and how to properly handle encrypted PDFs.
Comparison Table: PDF Encryption Solution Architectures
| Method | Pros | Cons | Best For |
|---|---|---|---|
| Client-Side Desktop Software | Direct user control, common tools, low initial cost | Poor centralized management, limited scalability, manual key handling | Small teams, ad-hoc encryption, low document volume |
| Server-Side DMS/IRM | Centralized control, automated policies, robust auditing, high throughput | Higher initial setup cost, requires dedicated infrastructure/software | Mid-to-large enterprises, consistent policy enforcement, high document volume |
| Cloud-Based Services | High scalability, reduced infrastructure burden, often API-driven | Reliance on third-party security, data residency concerns, subscription costs | Organizations leveraging cloud, rapid deployment, diverse access needs |
| Hybrid Solutions | Combines on-premise control with cloud scalability, flexible | Increased complexity in management, potential integration challenges | Large enterprises with specific compliance or legacy system needs |