
Securing sensitive documents is a paramount concern in both personal and professional life. Whether it's confidential business reports, personal financial records, or private correspondence, ensuring that this data remains inaccessible to unauthorized individuals is crucial. This is where the science of encryption algorithms comes into play, acting as the digital lock and key for our information.
Understanding the fundamental principles behind these algorithms empowers you to make informed decisions about protecting your digital assets. It's not just about setting a password; it's about the underlying mathematical processes that scramble your data into an unreadable format, only to be deciphered by someone possessing the correct key.
Table of Contents
Understanding the Basics of Data Encryption
At its core, data encryption is the process of transforming readable data (plaintext) into an unreadable format (ciphertext) using an algorithm and a secret key. This ciphertext can only be converted back into its original, readable form by using a corresponding decryption key. The strength of the encryption lies in the complexity of the algorithm and the secrecy of the key.
Key Concepts in Encryption
The two primary components are the algorithm, which is the set of mathematical rules used for encryption and decryption, and the key, which is a piece of information (often a string of characters or numbers) that controls the output of the algorithm. Without the correct key, even with the algorithm, the ciphertext remains indecipherable. This fundamental principle underpins all forms of file encryption.
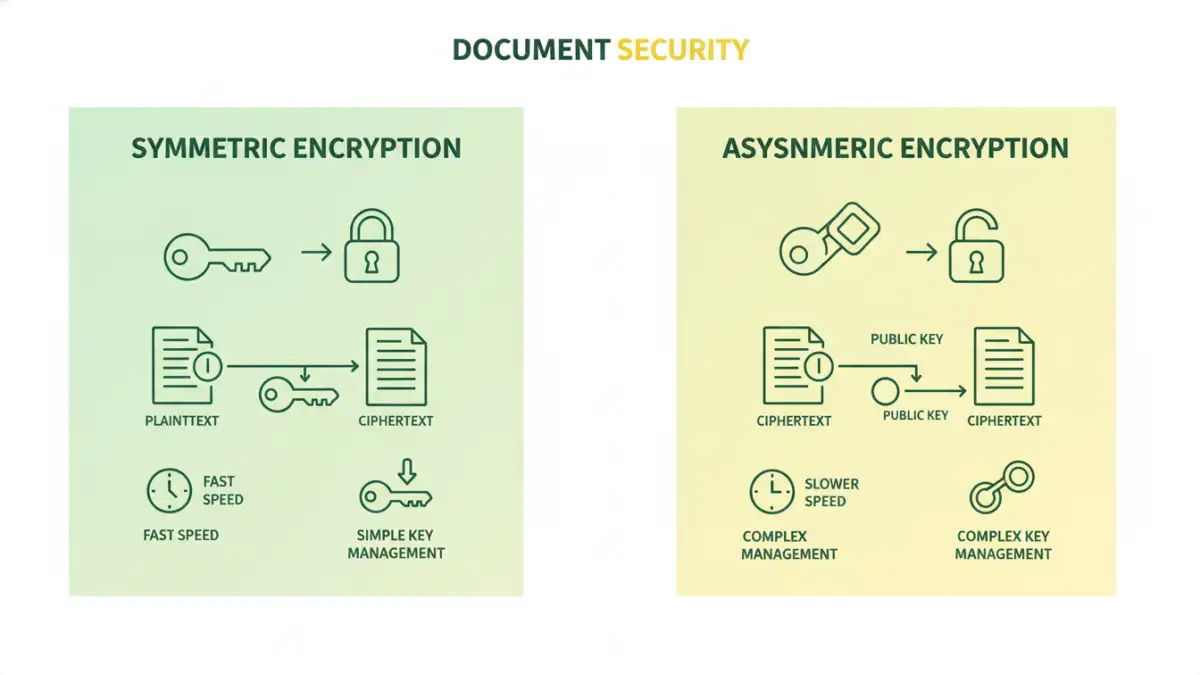
Symmetric Encryption: Speed and Simplicity

Symmetric encryption, also known as secret-key cryptography, uses a single, shared secret key for both encrypting and decrypting data. Imagine a locked box where the same key locks and unlocks it. This method is generally faster and less computationally intensive than asymmetric encryption, making it ideal for encrypting large volumes of data, like entire documents or databases.
Popular symmetric algorithms include AES (Advanced Encryption Standard), which is widely adopted for its security and efficiency, and older standards like DES (Data Encryption Standard) and Triple DES, though these are now considered less secure. The main challenge with symmetric encryption is secure key distribution: how do you safely share the secret key with the intended recipient without it being intercepted?
Asymmetric Encryption: Key Exchange and Authentication
Asymmetric encryption, or public-key cryptography, uses a pair of mathematically related keys: a public key and a private key. The public key can be freely shared and is used to encrypt data or verify a digital signature. The private key, however, must be kept secret by its owner and is used to decrypt data encrypted with the corresponding public key or to create a digital signature.
This method solves the key distribution problem of symmetric encryption. For example, if I want to send you an encrypted document, I would encrypt it using your public key. Only you, with your private key, can decrypt it. Asymmetric encryption is more computationally expensive, so it's often used for initial secure key exchange or for digital signatures to verify authenticity, rather than encrypting large files directly.
Comparing Key Encryption Algorithms
When we talk about encryption algorithms document protection, we are referring to the underlying mathematical functions that scramble the data. Different algorithms offer varying levels of security, speed, and suitability for different tasks. For instance, AES-256 is a current standard for symmetric encryption, offering robust security. On the asymmetric side, RSA and ECC (Elliptic Curve Cryptography) are commonly used.
The choice of algorithm often depends on the specific security requirements, performance needs, and the type of data being protected. For securing a single document with a password, a strong symmetric algorithm like AES is typically employed. For secure communication channels or verifying the sender's identity, asymmetric encryption plays a vital role.
Best Practices for Document Security
Implementing strong encryption is only one part of comprehensive document security. It's essential to combine robust encryption algorithms with sound security practices. Always use strong, unique passwords or passphrases for your encrypted files and consider using a reputable password manager to keep them secure and accessible.
Regularly update your software and operating system, as security vulnerabilities are often patched. Be cautious about where you store encrypted documents; cloud storage should be used with services that offer their own encryption, and sensitive documents should ideally be stored locally with strong encryption. Understanding the nuances of file encryption ensures your data remains private.
Comparison Table: Encryption Methods
| Method | Type | Key Management | Speed | Use Case Example |
|---|---|---|---|---|
| AES-256 | Symmetric | Single shared secret key | Fast | Encrypting large files, databases, full disk encryption |
| RSA | Asymmetric | Public/Private key pair | Slow | Secure key exchange (e.g., TLS/SSL), digital signatures |
| File Encryption Software (e.g., VeraCrypt, BitLocker) | Symmetric (often AES) | User-defined password/key file | Fast | Encrypting entire drives or specific folders/files |
| Password-Protected Documents (e.g., Word, PDF) | Symmetric (algorithm varies) | User-defined password | Moderate | Securing individual documents for sharing or personal storage |