
As businesses expand, the volume and sensitivity of the documents they handle inevitably increase. What might have been adequate security for a small team can quickly become a bottleneck or a significant vulnerability when operations scale up. I've seen this firsthand – a startup that relied on simple password protection for all its files suddenly found itself overwhelmed when its client base and internal data grew exponentially. The manual effort to manage those passwords became unsustainable, and worse, the security posture began to fray.
This isn't just about adding more passwords or encryption layers; it's about building a framework that can adapt. Assessing document security scalability means looking beyond immediate needs to anticipate future demands. It requires a strategic approach that balances robust protection with operational efficiency and cost-effectiveness. Failing to plan for this can leave a growing business exposed to data breaches, compliance issues, and reputational damage.
Table of Contents
Understanding Document Security Scalability
Document security scalability refers to the ability of a business's security measures to effectively handle increasing volumes of data, users, and access requests without compromising performance or security. For a growing business, this means the security system can expand or contract as needed, accommodating new employees, clients, and projects without requiring a complete overhaul. It's about building flexibility into your security infrastructure from the outset.
What 'Scalable' Really Means
In practical terms, scalability in document security means that your chosen solutions can manage a larger user base, a greater number of files, and more complex access control policies as your business grows. It implies that the system won't degrade in performance or become prohibitively expensive as your needs expand. This could involve moving from simple file-level encryption to more robust enterprise solutions.
Assessing Your Current Security Posture

Before you can scale, you need a clear picture of where you stand. This involves auditing your current document security practices, identifying weaknesses, and understanding your data flow. I often start by mapping out where sensitive documents are stored, who has access, and what controls are currently in place. This audit should cover everything from local drives and shared network folders to cloud storage and collaboration platforms.
Consider the types of documents you handle. Are they customer records, financial data, intellectual property, or employee PII? The sensitivity and regulatory requirements for each type will dictate the level of security needed. Understanding these nuances is crucial for building a scalable strategy that addresses all critical areas without over-investing in unnecessary protections.
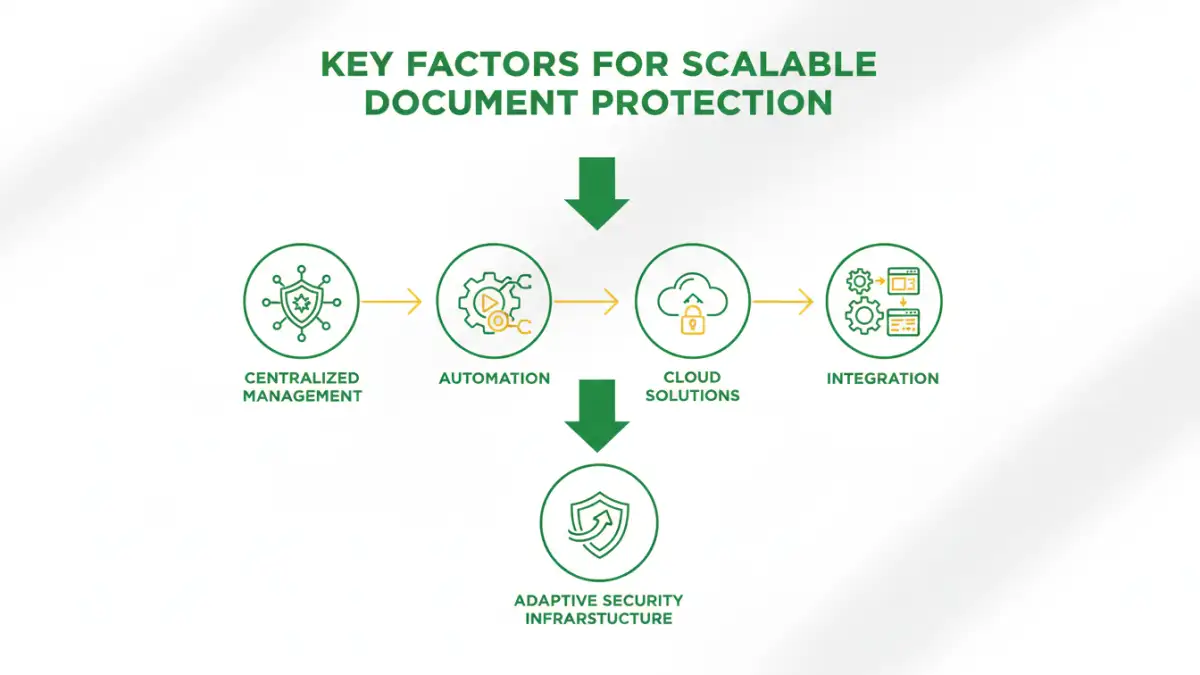
Key Factors for Scalable Document Protection
Several elements are fundamental to ensuring your document security can scale. Centralized management is paramount; systems that require individual configuration for each user or file quickly become unmanageable. Automated policies, such as access controls that adjust based on user roles or document classifications, are also essential.
The technology you choose plays a significant role. Cloud-based solutions often offer inherent scalability, allowing you to adjust resources as needed. However, ensure these solutions meet your compliance and data residency requirements. Furthermore, consider the integration capabilities of your security tools. Can they work seamlessly with your existing IT infrastructure, such as identity and access management systems?
User Access and Permissions Management
As your team grows, so does the complexity of managing user access. A scalable system should allow for granular control over who can view, edit, or share specific documents. Role-based access control (RBAC) is a critical component here, enabling administrators to assign permissions based on job functions rather than individual users. This simplifies onboarding and offboarding, and drastically reduces the risk of unauthorized access due to human error.
Implementation Strategies for Growth
When implementing new or upgraded security measures, phased rollouts are often the most effective approach for growing businesses. Start with the most critical data sets or departments and gradually expand. This allows your IT team to manage the transition smoothly and gather feedback for adjustments.
Consider a tiered security model. Not all documents require the same level of protection. You might use strong encryption and strict access controls for highly sensitive financial or PII documents, while applying less stringent measures for internal memos or public-facing marketing materials. This approach optimizes resources and ensures that critical data remains the primary focus of your security efforts.
Continuous Evaluation and Adaptation
The threat landscape is constantly evolving, and so are your business needs. What is secure today might not be tomorrow. Therefore, regular reviews and audits of your document security are non-negotiable. This includes staying informed about new threats, vulnerabilities, and emerging security technologies.
Gathering feedback from your users is also invaluable. Are the security measures hindering productivity? Are there any loopholes or workarounds being used? Addressing these concerns proactively can prevent security fatigue and ensure your systems remain effective and user-friendly. Document security scalability isn't a one-time project; it's an ongoing process of refinement and adaptation.
Comparison Table: Scalability Features of Document Security Solutions
| Solution Type | Scalability Features | Management Overhead | Typical Use Case |
|---|---|---|---|
| Basic File Encryption (e.g., OS built-in) | Limited; manual per-file or folder setup. Difficult to manage for many users/files. | High; requires individual user intervention. | Small teams, individual sensitive files. |
| Cloud Storage Security (e.g., Google Drive, SharePoint permissions) | Moderate to High; leverages cloud infrastructure. User/group management is key. | Moderate; centralized admin console. | Collaborative environments, general business documents. |
| Enterprise Digital Rights Management (DRM) | High; designed for large organizations. Granular control, policy enforcement, auditing. | Moderate to High; requires dedicated administration. | Regulated industries, IP protection, sensitive corporate data. |
| Data Loss Prevention (DLP) Solutions | High; can monitor and control data across multiple platforms and endpoints. Policy-driven. | High; complex setup and ongoing tuning. | Compliance, preventing data exfiltration, broad enterprise security. |